Disclaimer:Hey Guys, this post contains affiliate link to help our reader to buy best product\service for them. It helps us because we receive compensation for our time and expenses.
Scenario:-
As we all know that TLS 1.0 is outdated protocol, it was released somewhere in 1999 which is now no secure and most vulnerable hence for secure communications, this must be disabled on SQL server, application, web server and wherever applicable.
Also TLS 1.0 protocol welcomes ransomware attack which is so dangerous and capable of destroying whole IT infrastructure hence it is Primary work for DBA and application team to disable it and use upgraded version of TLS
Note:- Please make sure your application/database server should work post disabling TLS 1.0.
In this tutorial, we will walk through SQL side points that need to be taken care as well some of the application side points.
Please reach out to your respective application vendor for more information.
Transport Layer Security (TLS) encrypts data sent over the Internet to ensure that eavesdroppers and hackers are unable to see what you transmit which is particularly useful for private and sensitive information such as passwords, credit card numbers, and personal correspondence.
TLS 1.0 Default Settings:
By default, Windows clients and servers come with TLS (all version) enabled.
Its keys may or may not exist in the Registry editor. If keys do not exist in the registry path then it is said to be ENABLED and if keys exist then ENABLED/DISABLED depends on its value.
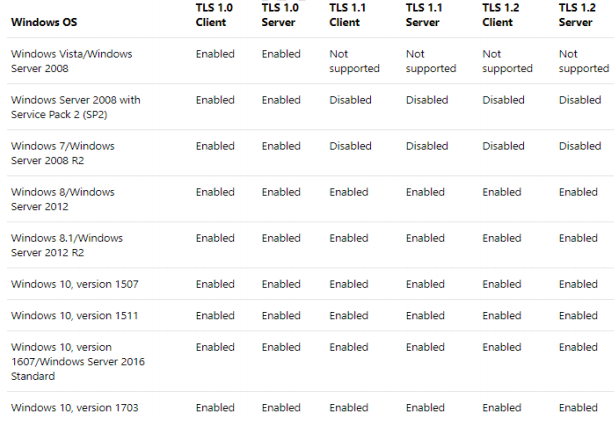
The following table displays the Microsoft Schannel Provider support of TLS protocol versions. Default:- ENABLED
Pre-checks [SQL server end]
- All database environments (Non-prod and Prod) must be patched with latest updates.
- Servers must have .NET 3.5.1 (3.5 SP1 ) and 4.6+ installed on it, follow below link to download the same.
https://www.microsoft.com/en-us/download/details.aspx?id=48130
https://www.microsoft.com/en-in/download/details.aspx?id=25150 - SQL server must be patched with latest SP top up with latest CU
- Update the SQL Native Client (SNAC)/ OBDC driver on all clients connecting to the SQL Server to the latest version.
- The latest version can be found here:
https://www.microsoft.com/en-us/download/details.aspx?id=50402
https://www.microsoft.com/en-us/download/details.aspx?id=36434
Pre-checks [Non-SQL server end]
- Severs (Web, application)etc must be patched with latest updates.
- Servers must have minimum .NET 3.5.1 (3.5 SP1 ) installed on it.
whoever uses SQL server managemt studio to connect SQL server database should have .NET 4.6+ installed on their workstation (desktop or laptop)
Follow below link to download the same.
https://www.microsoft.com/en-us/download/details.aspx?id=48130
https://www.microsoft.com/en-in/download/details.aspx?id=25150 - Update the SQL Native Client (SNAC)/ OBDC driver on all clients connecting to the SQL Server to the latest version.
The latest version can be found here:
https://www.microsoft.com/en-us/download/details.aspx?id=50402
https://www.microsoft.com/en-us/download/details.aspx?id=36434 - Check the connection string for ODBC connection, it should use updated ODBC driver.
Example:-
ODBC:DRIVER={SQL Server Native Client 11};.. - App team should check about other dependencies too from their end
so that post disabling TLS 1.0, application should communicate TLS 1.1 or TLS 1.2 or higher
To correctly disable TLS 1.0 follow the steps below:
>Install the Microsoft patch that allows you to continue using Remote Terminal Services or Remote Desktop after TLS 1.0 is disabled: https://support.microsoft.com/enus/kb/3080079
This should be the first step on your list, as missing this patch will
leave you unable to connect to your server after disabling TLS 1.0.
>Disable TLS 1.0 from the registry, using the registry editor. This one requires several sub-steps which you have to go through:
Open the
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\ registry key
If a TLS 1.0 key is present go inside, if not you will have to create a new Key and name it ‘TLS 1.0’
If the TLS 1.0 key exists, you should also have a key called ‘Client’ and one called ‘Server’ underneath, if not you will have to create them as you did in the previous step:
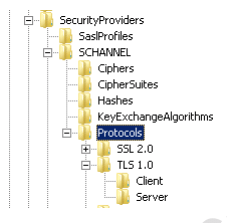
The next steps will have to be done both for the ‘Client’ and ‘Server’ keys as we want to disable TLS 1.0 when the OS is acting as a server (typically in the case of a website), but also when it is acting as a client and connecting to other resources that require secure connections. Go into the ‘Client’ key and create a DWORD (32 bit) entry and call this ‘Enabled’ and set its value to 0. Then repeat, and create a new DWORD (32 bit) entry for the ‘Server’ key and call it ‘Enabled’ and set the value to 0. This will disable TLS (all
versions) for both client and server.
> Now we have to enable versions 1.1 and 1.2 of TLS. For this, we need to create new keys called ‘TLS 1.1’ and ‘TLS 1.2’ underneath the ‘Protocols’ key.
> For each of the TLS 1.1 and TLS 1.2 keys, you should also create a ‘Client’ and a ‘Server’ key, as shown in the screenshot below:

>Once the key structure is created, you can proceed to creating a DWORD (32 bit) entry called ‘DisabledByDefault’ and set its value to ‘0’ in each of the four keys: TLS 1.1/Client, TLS 1.1/Server, TLS 1.2/Client and TLS 1.2/Server.
>Registry editor:-
Time to restart your server following these changes and you will see that the next connection attempt to resources that require https (secure connections) for your sites will be using TLS 1.1 or TLS 1.2
Reference link:-
https://blogs.msdn.microsoft.com/friis/2016/07/25/disabling-tls-1-0-on-your-windows2008-r2-server-just-because-you-still-have-one/
https://docs.microsoft.com/en-us/windows-server/security/tls/tls-registry-settings
Hope this helps!
Education is the best friend. An educated person is respected everywhere. Education beats the beauty and the youth.
Chanakya




You must be logged in to post a comment.